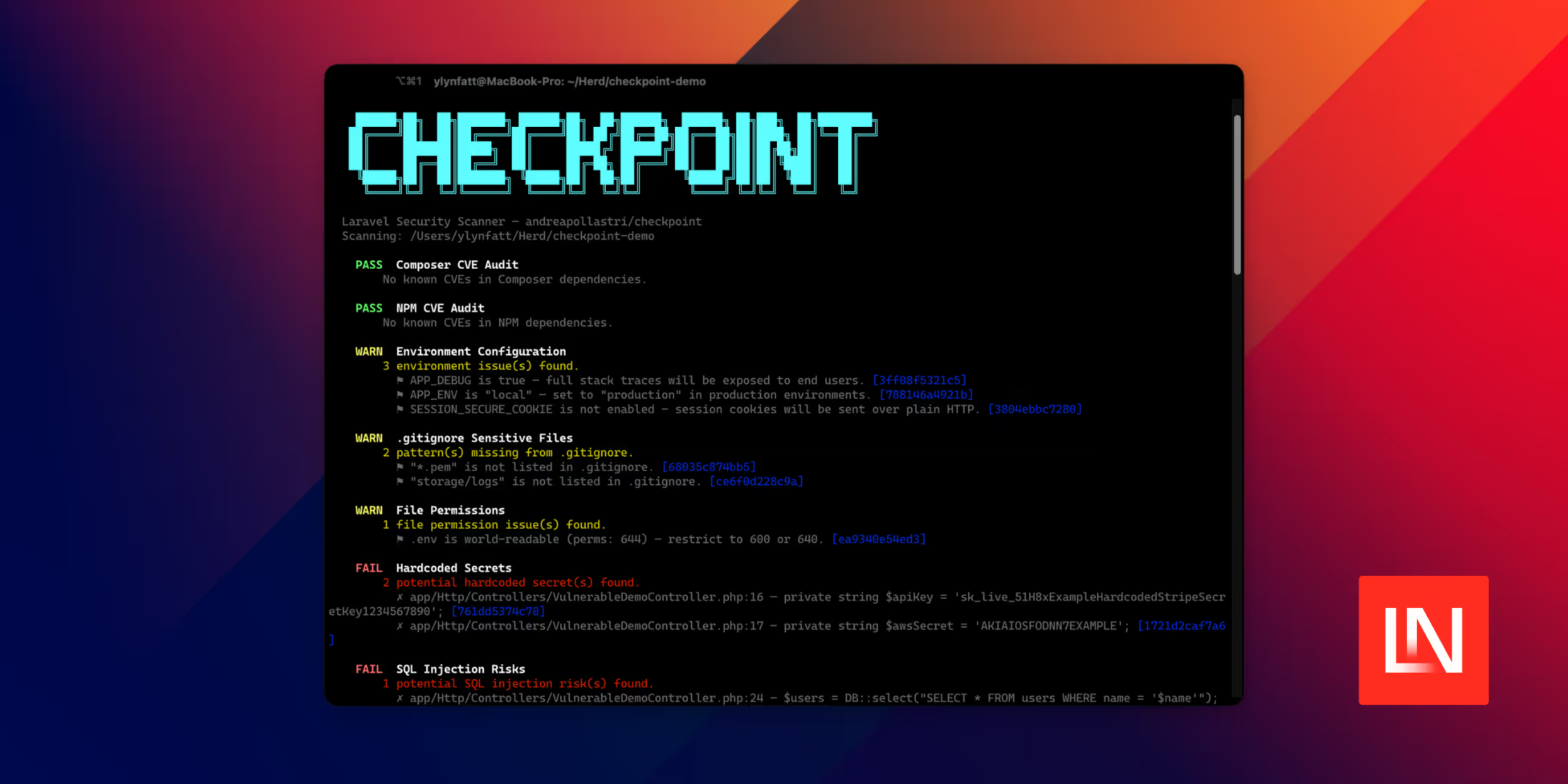
Spammers have one goal, to send as much spam as cheaply as possible with good IPs that are not blocked, and we've been hearing more and more reports of Laravel apps getting their SMTP credentials hacked and then the attackers using those to send junk.
This is not related to any vulnerability in Laravel itself. The issue is coming from improper server setups or not turning off debug mode.
Hide your .env file
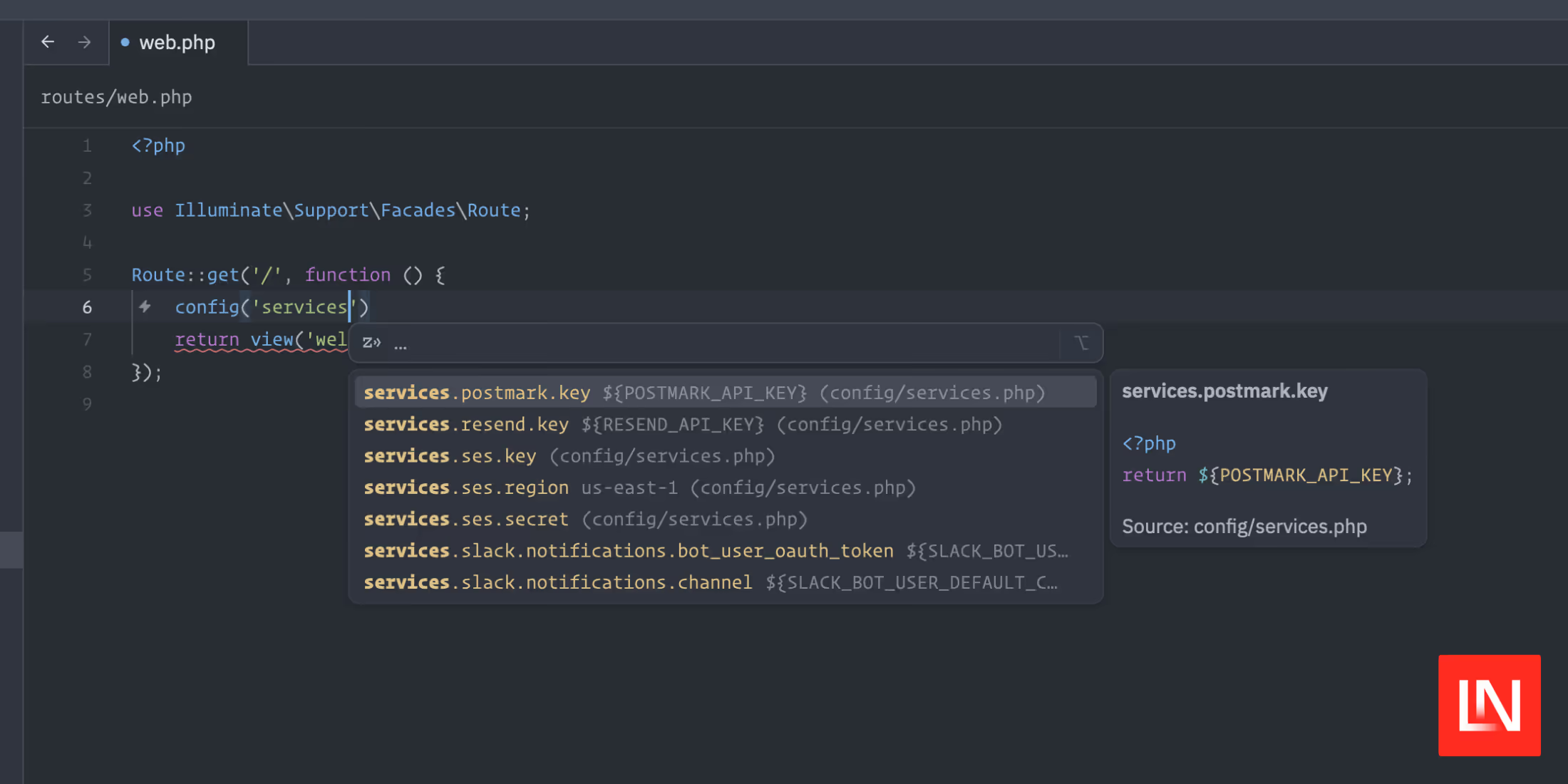
Laravel ships with a .env file that holds many configuration variables, including your database information and your mail server details; if this file becomes web-accessible, anyone can get your sensitive data and use those credentials.
By default, the directory structure of a default Laravel app has a public folder and that and only that should web-accessible.
In most situations, following the documentation on deployments section will set this up probably for you.
I've seen the majority of issues when developers try to install in a subdirectory and accidentally leave the .env file exposed. So double-check that for one, and I would highly suggest not installing it in a subdirectory unless you understand what you are doing. Instead, maybe consider using a subdomain.
Turn off debug mode
When you install a brand new Laravel app, debug mode is turned on for local development. Debug mode is beneficial for providing extra debugging tools and increased logs to help you develop new features and uncover potential problems. Then once you are ready to deploy, you need to change this setting and turn it off. It's helpful to have separate configuration files for your production environments, including leaning on configuring environment variables where you deem appropriate instead of adding config to a .env file.
APP_DEBUG=falseWith it left on, an attacker could figure out a way to get your app to generate an error, and then it might expose private credentials. The documenation outlines it in bold because it's super important:
In your production environment, this value should always be false. If the variable is set to true in production, you risk exposing your application's end users' sensitive configuration values.
Consider Using Laravel Forge
If you are not familiar with setting up servers, please consider using Laravel Forge, a first-party professional service for server management by the creators of Laravel. Forge takes the pain out of provisioning servers and fine-tunes them for Laravel. It also ensures proper application setup to ensure your .env is protected, along with many excellent managed features related to deploying a production Laravel application.