At Sqreen, we’re on a mission to help developers build more secure applications. But security is hard. It’s not always obvious what needs doing, and the payoffs of good security are at best obscure. Who is surprised when it falls off our priority lists? We’d like to offer a little help.
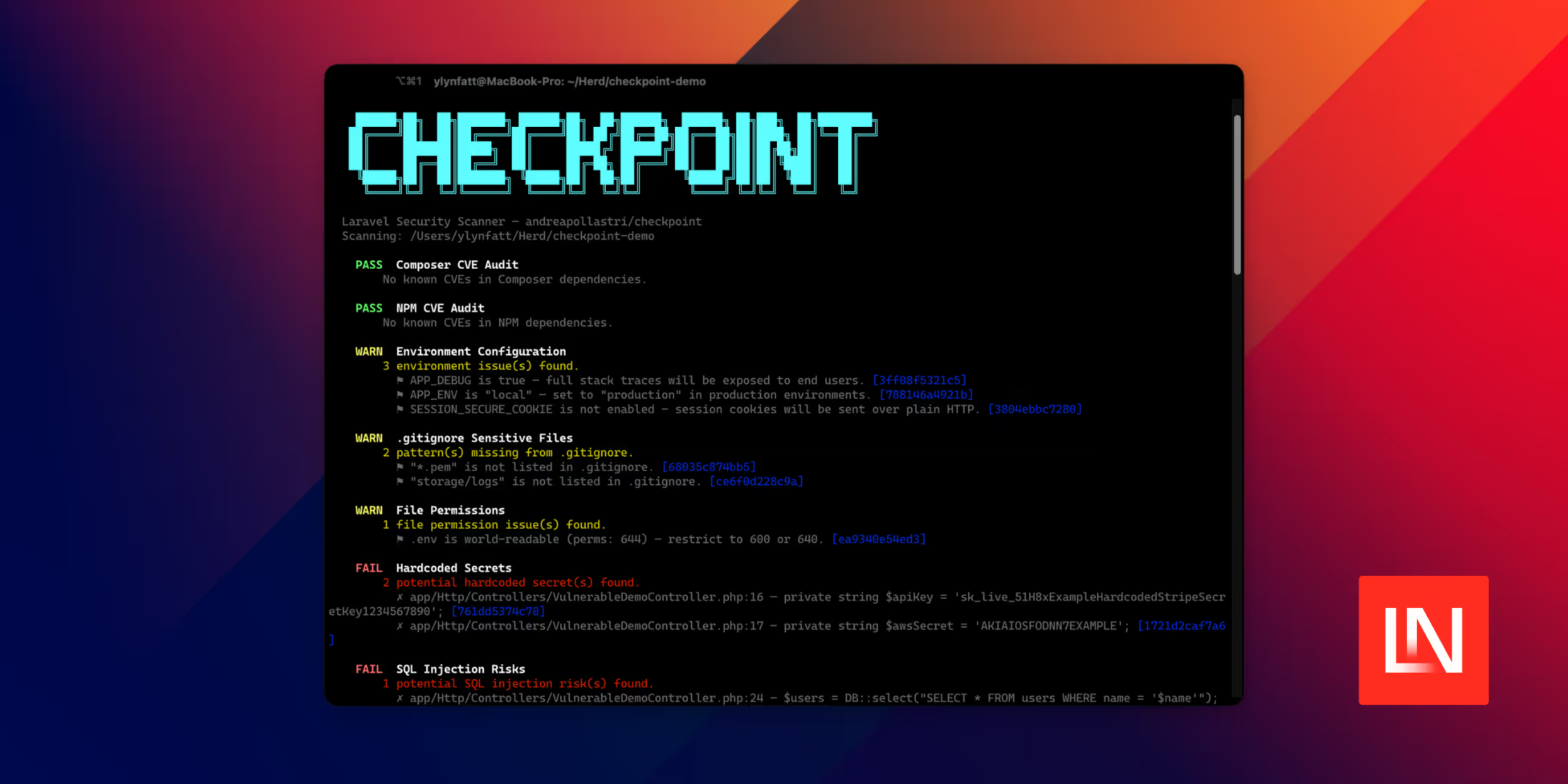
We created a Laravel Security Checklist to provide some guidance and to cover the best practices on securing your Laravel applications. Here are 10 tips from the checklist to get you started:
Code
✔ Filter and Validate All Data
Laravel’s Eloquent ORM uses PDO parameter binding to limit SQL injections. But Laravel also offers other ways to craft SQL queries. Regardless of where the data comes from, whether that’s a configuration file, server environment, GET and POST, or anywhere else, do not trust it. Filter and validate it!
Read more:
✔ Invalidate Sessions When Required
After any significant application state change, such as a password change, password update, or security errors, expire and destroy the session.
Read more:
✔ Store Passwords Using Strong Hashing Functions
Ensure that all passwords and other potentially sensitive data are hashed, using robust hashing functions such as bcrypt. Don’t use weak hashing functions, such as MD5 and SHA1. Laravel comes with a native hash mechanism using Bcrypt and Argon2. Use them!
Read more:
- Hashing in Laravel
- Use Bcrypt or Scrypt Instead of SHA* for Your Passwords, Please!
- The Dangers of Weak Hashes
✔ Use Laravel’s built-in encryption
Laravel comes with a built-in encryption mechanism and we highly recommend you use that one instead of building your own. As of PHP 7.2, older encryption libraries have been deprecated, such as Mcrypt. However, PHP 7.2 supports the far better Libsodium library instead. If you want to use a different encryption library, take a look at Libsodium.
Read more:
- PHP 7.2: The First Programming Language to Add Modern Cryptography to its Standard Library
- Libsodium
- Laravel Encryption
Infrastructure
✔ Check Your SSL / TLS Configurations
Ensure that your server’s SSL/TLS configuration is up to date and correctly configured, and isn’t using weak ciphers, outdated versions of TLS, valid security certificates without weak keys, etc, by scanning it regularly.
Read more:
✔ Rate Limit Requests to Prevent DDoS Attacks
To stop users attempting to perform brute force login attacks and overwhelm your forms, use tools such as Fail2Ban to throttle requests to acceptable levels.
Read more:
✔ Log All The Things
Regardless of whether you’re logging failed login attempts, password resets, or debugging information, make sure that you’re logging, and with an easy to use, and mature package, such as Monolog.
Read more:
Protection
✔ Send All Available Security Headers
There are several security headers that you can use to make your websites and web-based applications more secure, for minimal effort. These include HSTS, X-XSS-Protection, X-Frame-Options, X-Content-Type-Options, and a Content Security Policy. Ensure that they’re being configured correctly and sent in your request responses.
Read more:
- Use these Five Security Headers To Create More Secure Applications
- SecurityHeaders
- PHP header function
- Hardening Your HTTP Security Headers
✔ Have a Content Security Policy
Whether you have a one page, static website, a large static website, or a sophisticated web-based application, implement a Content Security Policy (CSP). It helps to mitigate a range of common attack vectors, such as XSS.
Read more:
- Content Security Policy (CSP) via MDN web docs
- Content Security Policy (CSP) via the Google Chrome extensions documentation
- CSP Evaluator
- Content Security Policy (CSP) Validator
✔ Monitor your application security
Monitor your application security for suspicious behaviors and attacks. Knowing when your application is starting to get attacked is key to protect it before it’s too late.
Want to read the full checklist? Download your copy here!
Many thanks to Sqreen for sponsoring Laravel News this week.