Two malicious versions of the popular axios HTTP client library were published to npm on March 30–31, 2026, after an attacker compromised a maintainer's account. The affected versions, axios@1.14.1 and axios@0.30.4, installed a remote access trojan (RAT) on developer machines across macOS, Windows, and Linux.
Axios is one of the most widely used JavaScript HTTP clients and is a common dependency in Laravel projects using Vite, Inertia, or any Node-based build pipeline.
What Happened
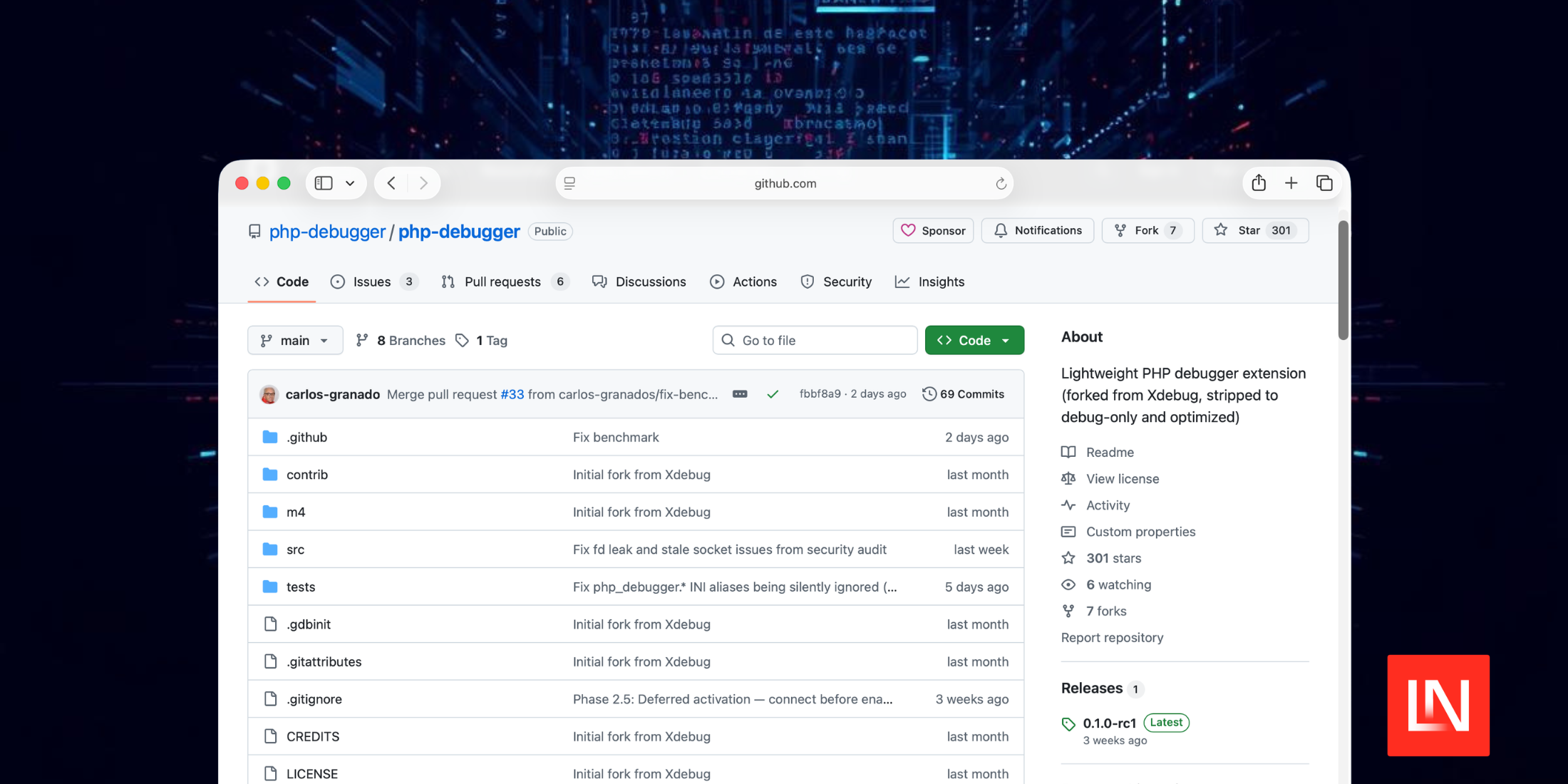
According to the StepSecurity blog post the attacker hijacked the npm account of the primary axios maintainer (jasonsaayman), changing the registered email to a Proton Mail address. Using this access, they published two new versions that added a single fake dependency: plain-crypto-js@4.2.1.
That package masqueraded as the legitimate crypto-js library but included an obfuscated postinstall script (setup.js) that acted as a cross-platform RAT dropper. The only file changed in axios itself was package.json, every other file across 85+ source files remained identical to the clean release.
How the Attack Worked
The attacker never touched the Axios source code. Instead, both release branches received a single new dependency: plain-crypto-js@4.2.1. No part of the codebase imports it. The package exists solely to run a postinstall script that drops a cross-platform RAT onto the developer's machine.
The staging was precise. Eighteen hours before the axios releases, the attacker published a clean version of plain-crypto-js under a separate npm account to build publishing history and dodge new-package scanner alerts. Then came the weaponized 4.2.1. Both release branches hit within 39 minutes. Three platform-specific payloads were pre-built. The malware erases itself after execution and swaps in a clean package.json to frustrate forensic inspection.
StepSecurity, which identified the compromise alongside Socket, called it among the most operationally sophisticated supply chain attacks ever documented against a top-10 npm package.
How this affects Laravel
This is not a Laravel vulnerability, but they announced they are taking proactive steps to protect the community from this supply chain attack, and telling people:
If you installed or updated axios in the last 24 hours, scan your machine.
Here is what the Laravel has done:
- Pinned axios to safe versions in laravel/laravel
- laravel/installer now runs package installs with --ignore-scripts by default
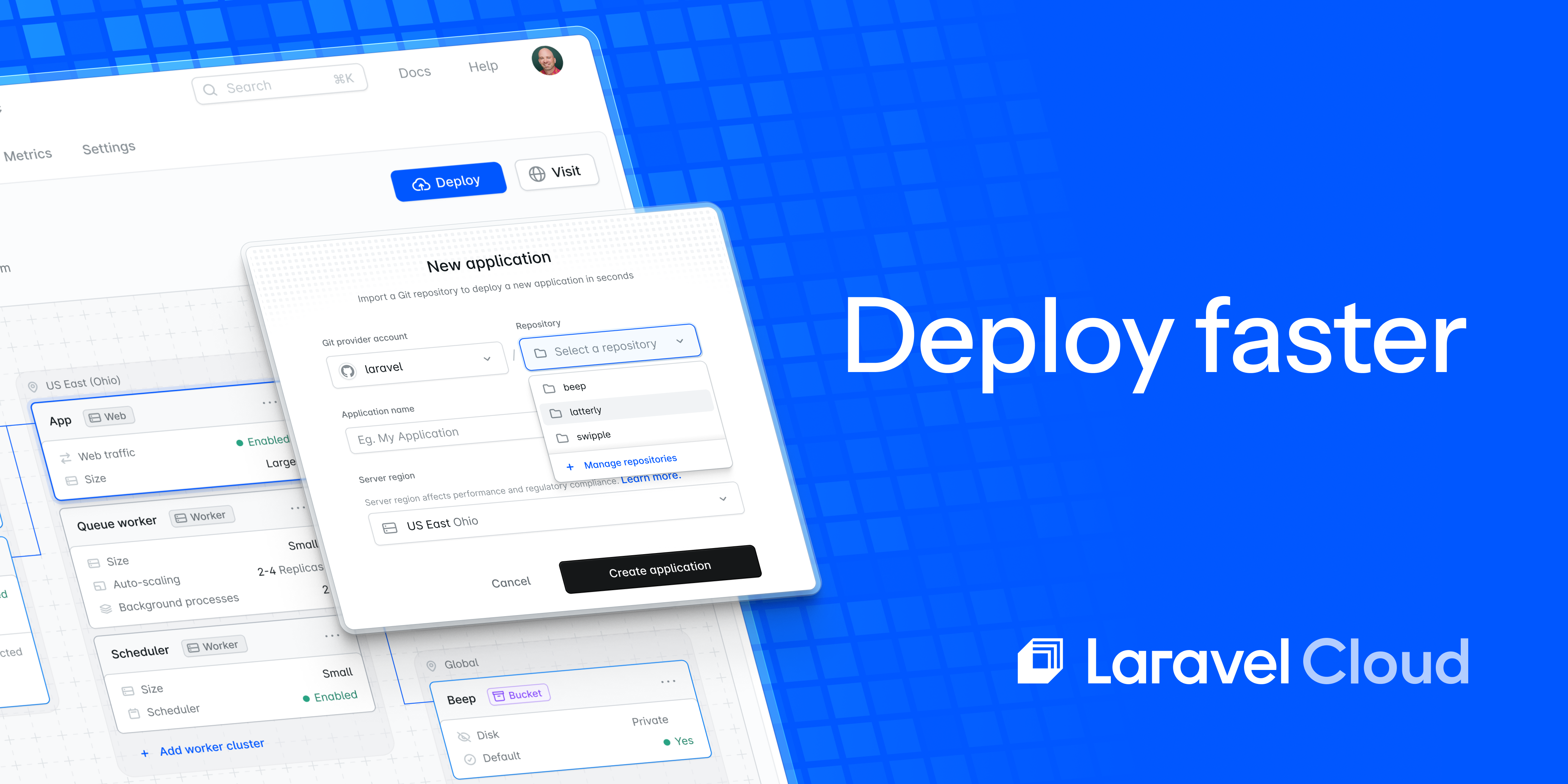
- Blocked the attacker's domain across Laravel Cloud
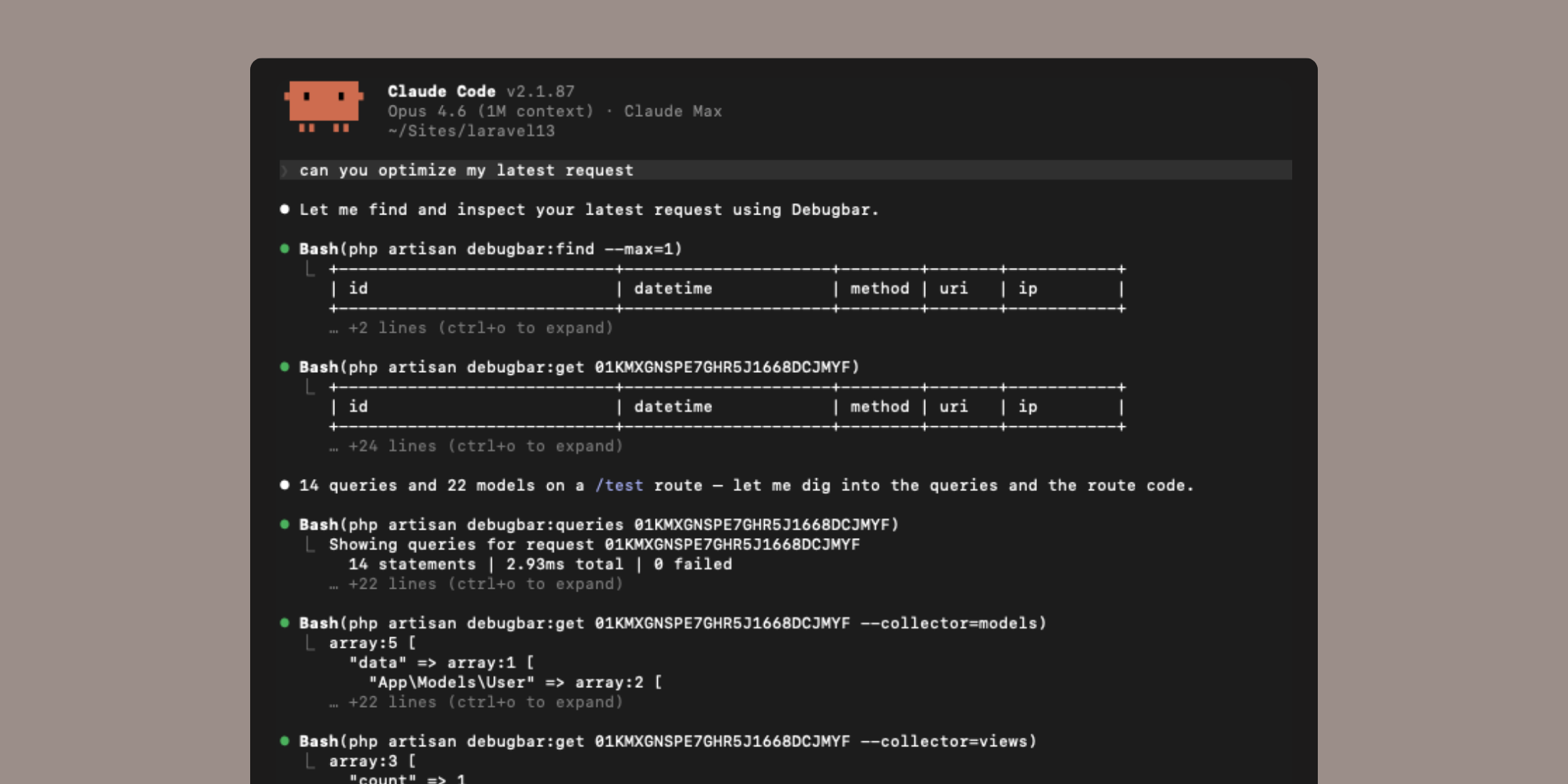
Pushpak also shared a prompt you can use to scan your local computer to check for any vulnerable installs.
What You Should Do
If you installed axios@1.14.1 or axios@0.30.4 during the window they were available, treat any machine that ran npm install as compromised. StepSecurity recommends:
- Remove the poisoned packages and pin to a safe version (
axios@1.14.0or0.30.3) - Check for RAT artifacts at the file paths listed above
- Rotate all credentials and tokens on affected machines
- Reformat compromised systems